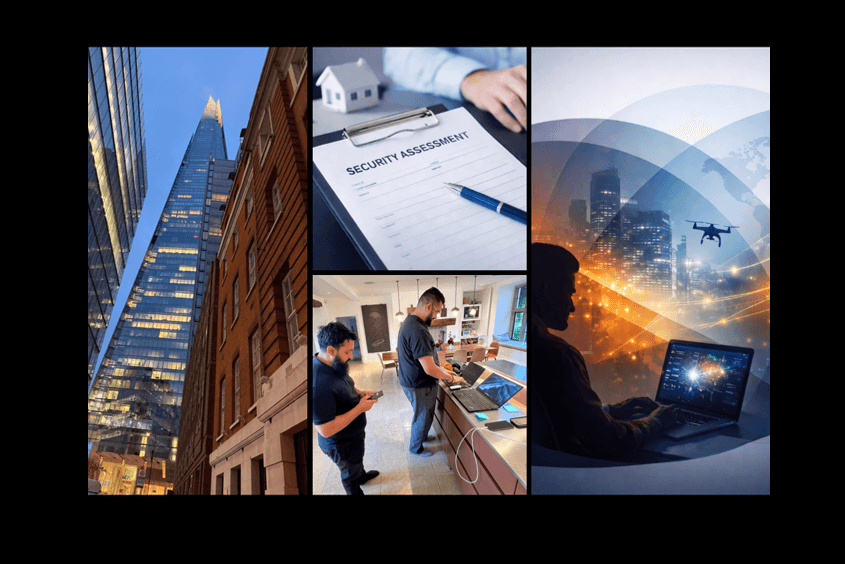
During a TSCM/cyber tasking on a residential premises last week the client spoke to our telecoms engineer about a role out of new telephone systems in their new London offices. Our engineer explained that when having sensitive business conversations, sharing confidential financial information or receiving payments over business calls, it is essential to secure these calls.
Our engineer explained that there are various options available including Voice over Internet Protocol (VoIP) telephone systems, VoIP calling holds endless advantages from a price and accessibility point of view, and now more than ever, VoIP calling provides a significant level of high security to protect businesses. However, it’s important they are configured correctly.
VoIP solutions with sophisticated controls can reduce the potential risk of external disruption. There have been times when conducting a TSCM inspection we could easily access voicemails and conference calls due to the way the system had been set up. Our engineer recommends the below key points as essential (but are not limited to) when installing and setting up the VoIP system.
1.Ensure your VoIP provider can offer call encryption as this will defend against any unauthorised use of your business phone line
2.Ensure you have secure VoIP with Two Factor Authentication (2FA) in place, this will create an instant barrier. 2FA adds an extra layer of security and makes your data and customer communications twice as protected compared to a one-step, standard password login
3.Ensure that Voicemail passwords are changed from their default. If others can access data, ensure audit trails are enabled.