Services
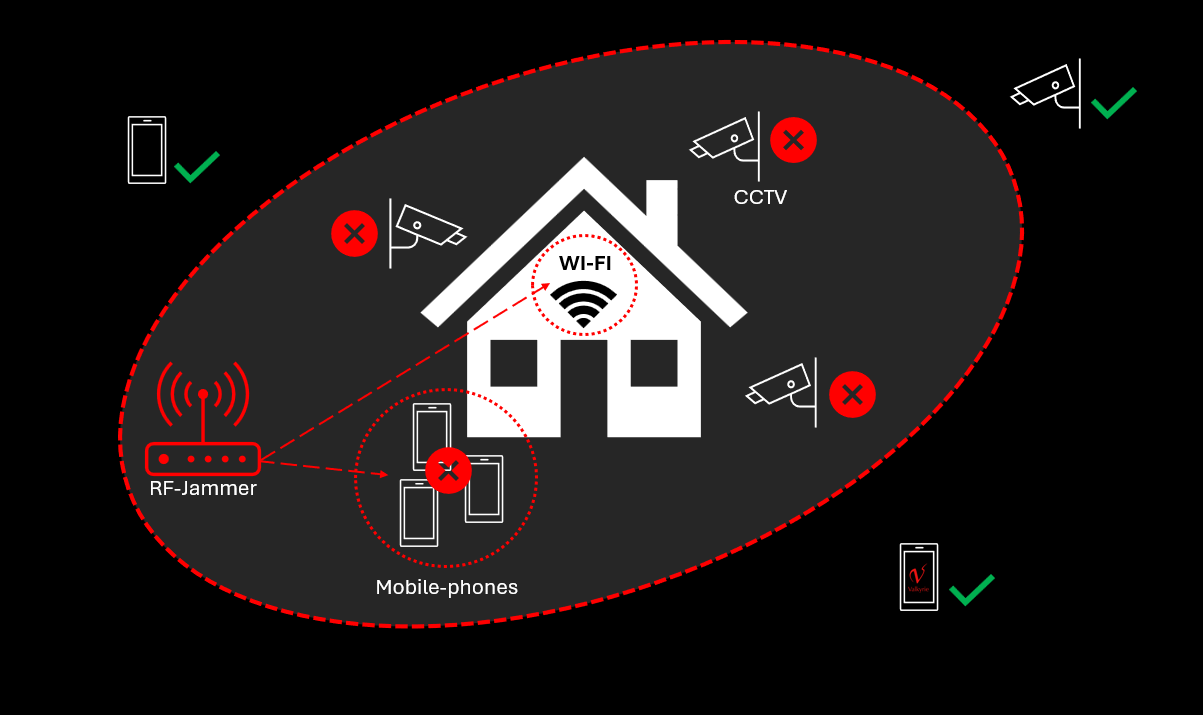
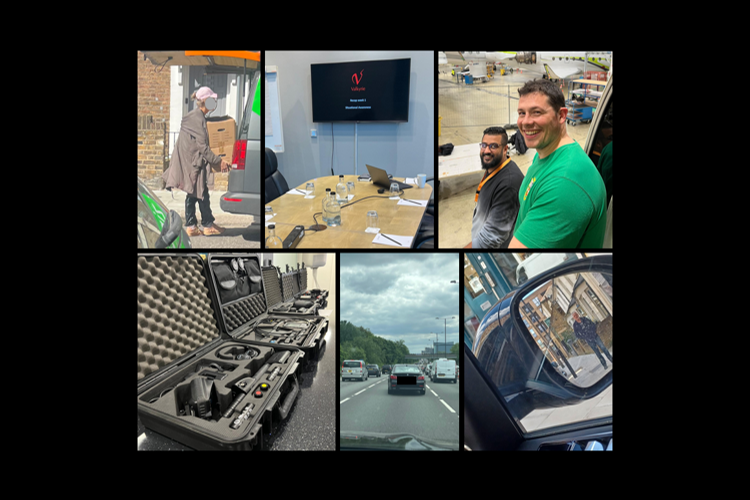
Valkyrie’s expertise spans a comprehensive range of security services to safeguard our clients, from technical surveillance countermeasures (TSCM) and cyber security, to crisis management and complex investigations. Our holistic approach integrates cutting-edge technology with proven field tactics to ensure unparalleled protection
Heading
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
Who we work with
Valkyrie works with individuals, companies and government bodies on a range of security concerns. Our client-focused approach means that your specific security needs — whether your concerns involve personal, business, or sensitive state-level matters — are in safe hands

Corporate
Facing an array of distinctive challenges, companies and corporate entities benefit from our proactive and reactive consultations. Our expertise extends from incident management to comprehensive risk assessments, investigations and organisation wide training; we also support various partner organisations to help deliver on their clients objectives. Our services safeguard corporate interests against evolving threats.

Government
Collaborating with government agencies worldwide, Valkyrie supports the delivery of diplomatic protection and governmental security needs. Services include large-scale TSCM testing, risk assessments, cyber and physical penetration testing, and white-label access systems. Trusted by global authorities, Valkyrie provides discreet and effective security for governmental protection.

Individuals
Valkyrie offers tailored solutions for individuals with diverse security concerns and complex problems. Our clientele includes high-net-worth individuals and professionals facing heightened scrutiny; we identify risks to their privacy and security and put in place discreet solutions to protect them, their families, and their assets. This considers all aspects of their physical and digital security, from cyber forensics to online threats, physical risks and access system installation; our services meet their unique needs. Trust Valkyrie for proactive security solutions safeguarding what matters most.
News
Stay informed with the latest insights, expertise and innovations in the world of security with Valkyrie’s news, reports and white papers
Get in touch
Send us an enquiry and one of our advisors will be in touch with you shortly